⚠️ Museum post
This post is a piece of history of this blog, imported from older times where practices were different. It remains online for the sake of sharing information, but should not be used at face value anymore.
I’m currently staying in Luxembourg for the Hack.lu event and got pretty surprised when I attempted to connect on the hotel’s WiFi:
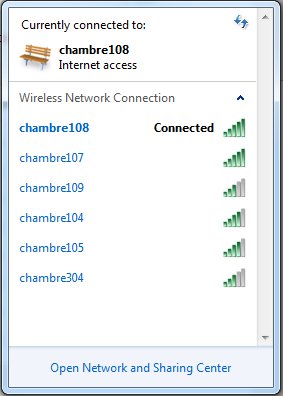
One access point per room ?! Well, that’s a first for me. It got even more intriguing when I had a look around in the room and couldn’t see any network equipment besides the phone:

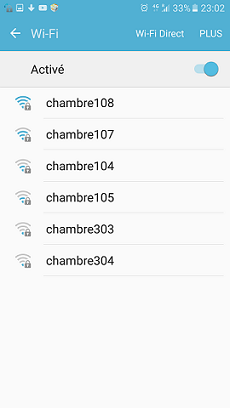
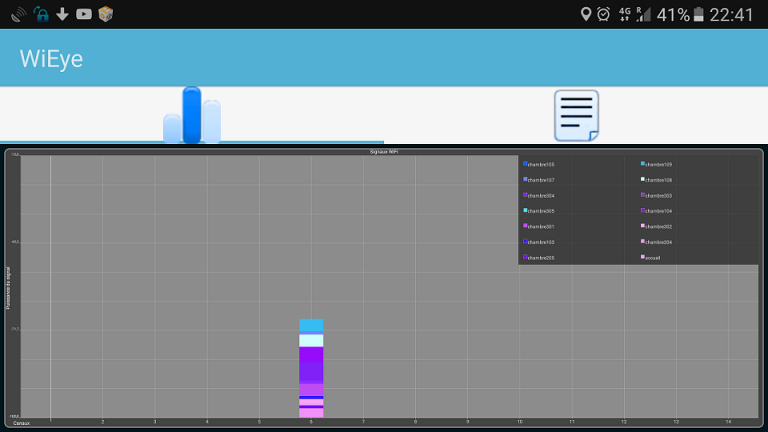
Moving around with WiEye open to look at the signal strength evolution points towards direct proximity of the phone, but I still can’t see any device that looks like an AP. Maybe it is hidden behind the wooden furniture of the room?
The TV uses a satellite decoder, so I doubt it’s the one broadcasting the WiFi. There’s still the possibility it’s a single AP somewhere broadcasting multiple network using some crazy configuration. A quick inspection with WiEye using my smartphone shows it’s not the case:
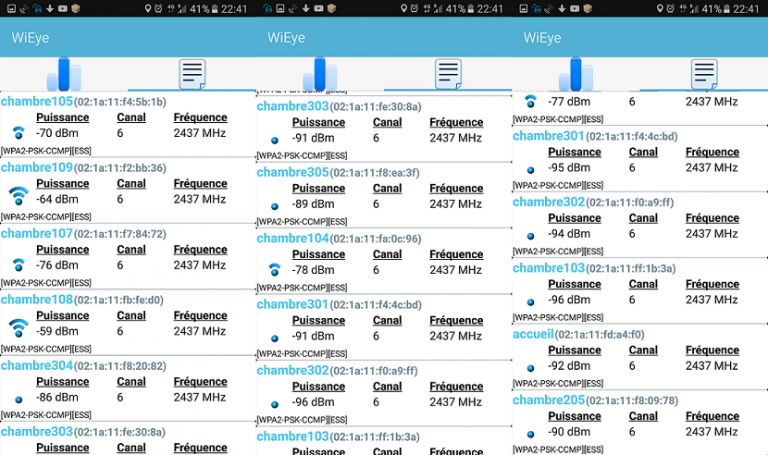
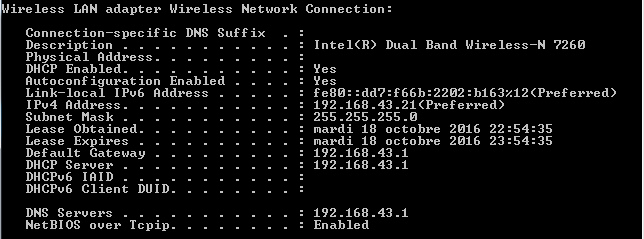
However, that MAC OUI looks familiar. A little Google search later, the plot thickens: all these access points are Android devices in AP mode ! Often, whenever there’s an AP, there’s a web interface. Okay, let’s have a look at the computer’s IP settings:
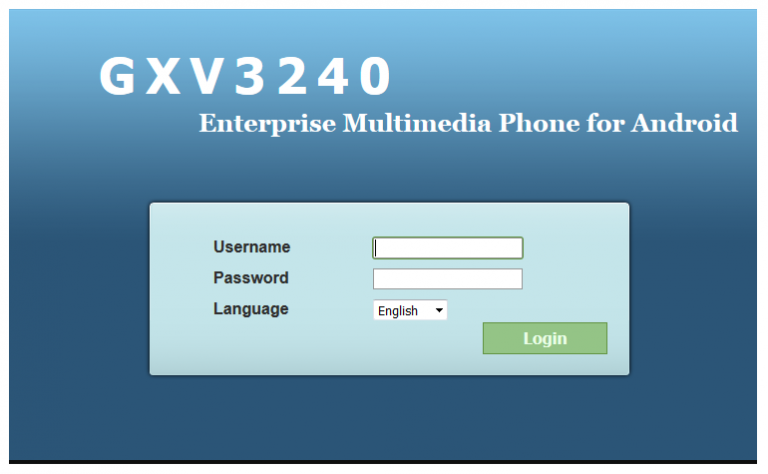
I take my chance and try to access the GW IP address with a browser. Bingo ! I had the AP in front of my eye since the beginning… It’s a friggin’ desktop phone running Android and acting as an access point:
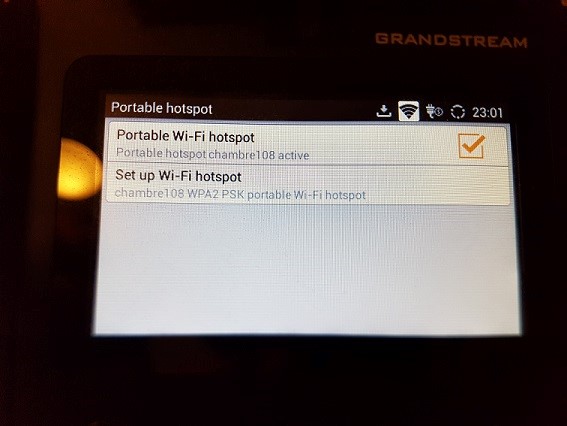
You can even browse the web from the phone ! Those glorious 56k modems days where you couldn’t phone and browse are definitely gone.

Then, what’s that little black device between the wall Ethernet plug and the phone ? It’s a Long Reach Ethernet to standard Ethernet adapter, basically used to transport Ethernet & Power over long distances:

Had I had a PoE splitter with me, I could have connected my laptop directly to the hotel’s network. I don’t know what to make of it. On one hand, I find that an extremely clever way to deploy WiFi without having a single overloaded AP for all the rooms, like you often see. We’ve all experienced that situation where a hotel WiFi was completely unusable due to overcrowding.
But, on the other hand, it’s deployed in a totally unsecure way. I’m what you could call a “white hat” guy. I like to understand how things work and how they can be broken, but I don’t take any pleasure in breaking other people’s stuff just for the hell of it. But someone with a more evil approach of life could easily mess up the complete network.
Just imagine how many credentials could be sniffed with a Rogue IPv6 RA + TLS intercept + NAT64/DNS64 setup…
Disclaimer: I willingly didn’t disclose the name of hotel nor its location, and stripped EXIF data from the photos. I’m not encouraging anyone to hack into anybody’s hotel, I just want to highlight how easily a good idea can be implemented in a very insecure way. Don’t be that guy every traveler hates!
